Correct Answer

verified
Correct Answer
verified
Multiple Choice
____ prevents unauthorized users from creating, modifying, or deleting information.
A) Availability
B) Integrity
C) Confidentiality
D) Risk management
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
The ____ describes the system at the beginning of system operation and includes the results of performance and acceptance tests for the operational system.
A) functional baseline
B) operational baseline
C) allocated baseline
D) product baseline
F) A) and D)
Correct Answer

verified
Correct Answer
verified
Short Answer
____________________ means that in normal operating conditions, any transaction that occurs on the primary system must automatically be mirrored to the hot site.
Correct Answer

verified
Correct Answer
verified
Short Answer
MATCHING Identify the letter of the choice that best matches the phrase or definition. a.private key encryption f.transference b.public key encryption g.attack c.CIA h.security d.threat i.CM e.mitigation j.software reengineering -In risk control, this shifts the risk to another asset or party.
Correct Answer

verified
Correct Answer
verified
True/False
Although the procedures for corrective maintenance and adaptive maintenance are alike, minor corrective maintenance requires more IT department resources than minor adaptive maintenance.
B) False
Correct Answer

verified
Correct Answer
verified
True/False
When network traffic is encrypted, it is invisible and its content and purpose are masked. _________________________
B) False
Correct Answer

verified
Correct Answer
verified
True/False
As enterprise-wide information systems grow more complex, configuration management becomes less and less useful.
B) False
Correct Answer

verified
Correct Answer
verified
Multiple Choice
The ____ is responsible for assigning maintenance tasks to individuals or to a maintenance team.
A) user
B) programmer
C) systems review committee
D) system administrator
F) A) and D)
Correct Answer

verified
Correct Answer
verified
True/False
Successful, robust systems often need the most support because users want to learn the features, try all the capabilities, and discover how the system can help them perform their business functions.
B) False
Correct Answer

verified
Correct Answer
verified
True/False
Both adaptive and perfective maintenance activities decrease in a dynamic business environment. _________________________
B) False
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Risk ____ analyzes the organization's assets, threats, and vulnerabilities.
A) assessment
B) management
C) identification
D) control
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Risk ____ measures risk likelihood and impact.
A) assessment
B) management
C) identification
D) control
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
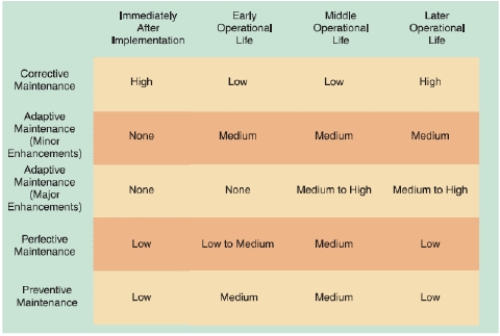
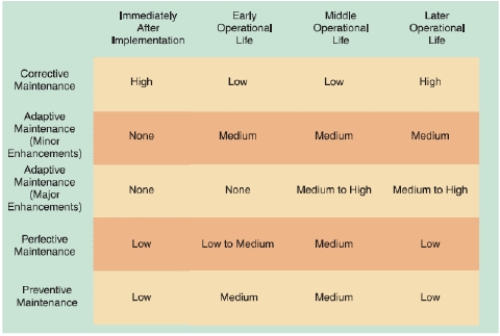 -As shown in the accompanying figure, ____ when it becomes clear that the company plans to replace the system.
-As shown in the accompanying figure, ____ when it becomes clear that the company plans to replace the system.
A) adaptive, corrective, and perfective maintenance expenses all increase rapidly
B) perfective maintenance expenses increase rapidly, but adaptive and corrective maintenance typically decrease
C) adaptive and corrective maintenance expenses increase rapidly, but perfective maintenance typically decreases
D) adaptive, corrective, and perfective maintenance expenses all decrease rapidly
F) None of the above
Correct Answer

verified
Correct Answer
verified
True/False
The main objective of user training is to show users how to become service desk staff members.
B) False
Correct Answer

verified
Correct Answer
verified
True/False
Configuration management is sometimes referred to as change control.
B) False
Correct Answer

verified
Correct Answer
verified
Short Answer
MATCHING Identify the letter of the choice that best matches the phrase or definition. a.private key encryption f.transference b.public key encryption g.attack c.CIA h.security d.threat i.CM e.mitigation j.software reengineering -A process for controlling changes in system requirements during software development.
Correct Answer

verified
Correct Answer
verified
Multiple Choice
____ means examining the whole in order to learn about the individual elements.
A) Synthesis
B) Risk management
C) Analysis
D) Risk identification
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
 -Adaptive maintenance ____.
-Adaptive maintenance ____.
A) adds enhancements to an operational system and makes the system easier to use
B) diagnoses and corrects errors in an operational system
C) involves changing an operational system to make it more efficient, reliable, or maintainable
D) requires analysis of areas where trouble is likely to occur in order to avoid problems
F) B) and C)
Correct Answer

verified
Correct Answer
verified
True/False
Using a release methodology increases the documentation burden. _________________________
B) False
Correct Answer

verified
Correct Answer
verified
Showing 61 - 80 of 112
Related Exams